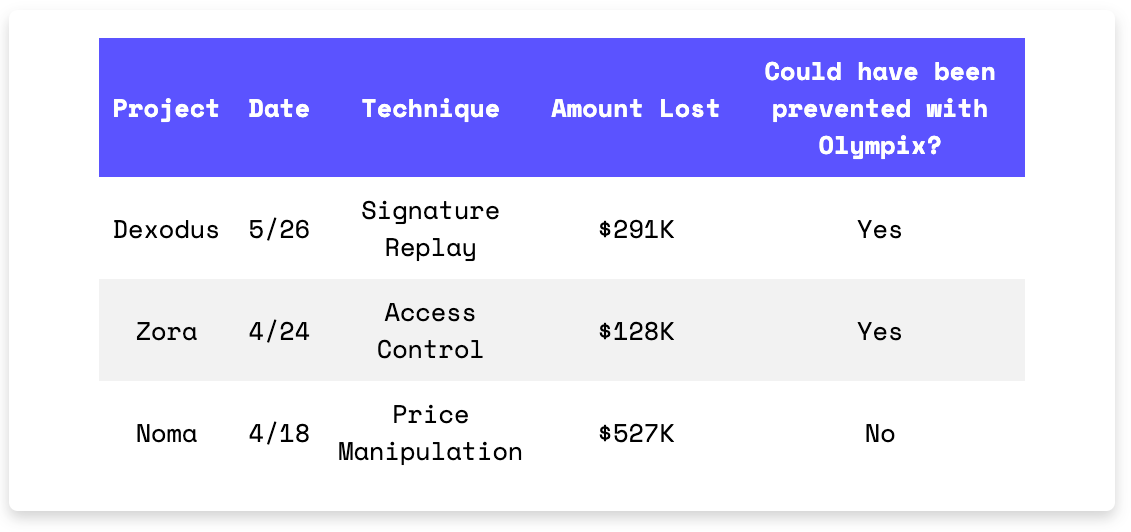
$419K Could Have Been Saved If Only They Used Olympix!
June 3, 2025
In Brief
Dexodus lost $291K in a signature replay attack.
Zora was exploited for $128K after missing access controls in their token claim function.
Numa suffered a $527K loss due to a flash loan price manipulation.
Hacks Analysis
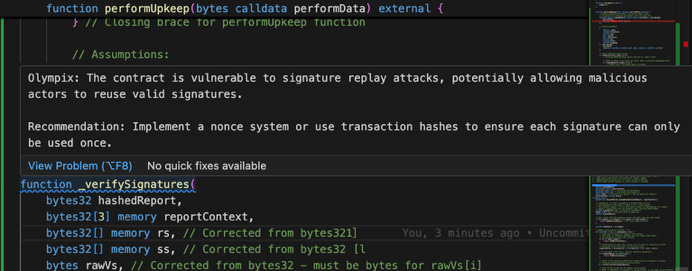
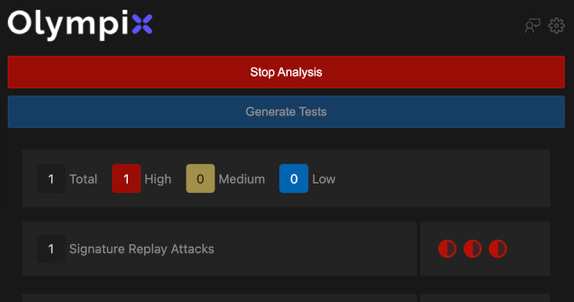
Dexodus | Amount Lost: $291K
On May 26, the Dexodus Finance exploit on Base chain resulted in a $291K loss due to a signature replay attack. The attacker used a valid but outdated Chainlink price report via the performUpkeep() function, which lacked proper timestamp validation. This allowed them to open a 100x leveraged long position on ETH at an artificially low price of $1,816. They then closed the position at the current market price of $2,520 within the same transaction, profiting approximately $291K.
Exploited Contract (Verifier Proxy on Base): 0xde1a28d87afd0f546505b28ab50410a5c3a7387a
Transaction: 0x6ffb494293fc5c32c5a6ab7dc3fff1fcc6e90fba9a6d6e486ba0a15ce518147e
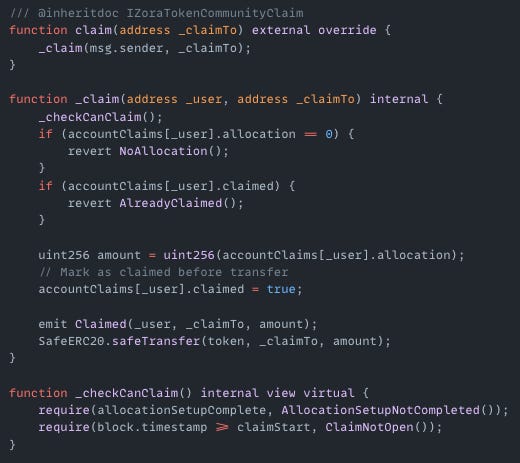
Zora | Amount Lost: $128K
On April 24, the Zora exploit on Base chain resulted in a $128K loss. The root cause of the exploit was that Zora’s TokenCommunityClaim contract’s claim() function didn’t have proper access control and allowed the attacker to input any _claimTo address. The attacker targeted addresses with unclaimed token allocations and used them as the _user parameter, while setting _claimTo to a contract they controlled. This allowed the attacker to reroute airdropped tokens to their own address.
Exploited Contract (Zora: Token Community Claim on Base): 0x0000000002ba96c69b95e32caab8fc38bab8b3f8
Transaction: 0xf71a96fe83f4c182da0c3011a0541713e966a186a5157fd37ec825a9a99deda6
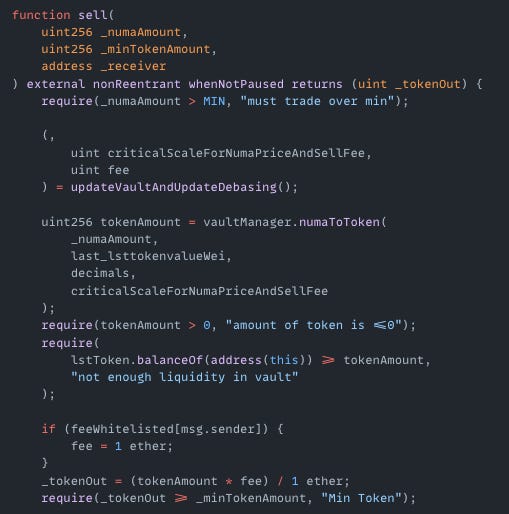
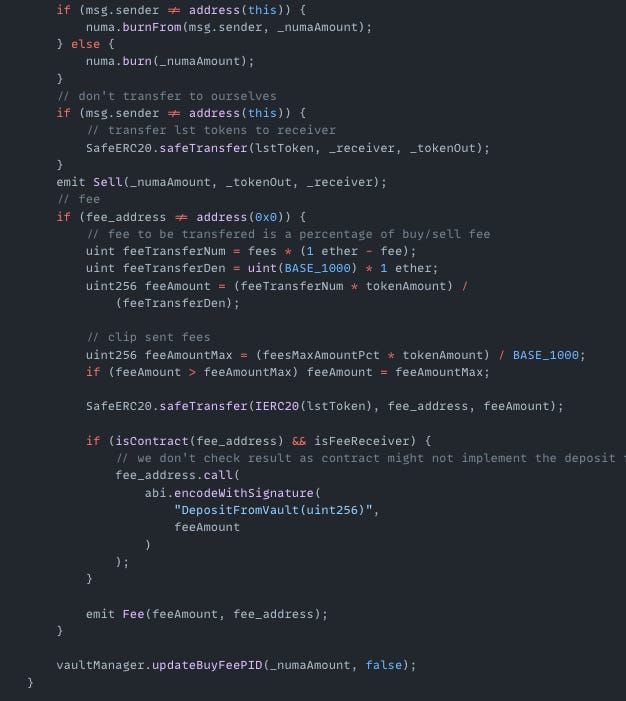
Numa | Amount Lost: $527K
On April 18, the Numa exploit on Arbitrum resulted in a $527K loss due to a price manipulation exploit. The attacker used a flash loan to interact with the sell() function, which burned NUMA tokens and reduced total supply. This increased the token’s internal price. The attacker then locked the manipulated price using lockNumaSupply(). With the inflated value fixed, they borrowed assets from the protocol at favorable rates and withdrew them for profit.
Exploited Contract (on Arbitrum): 0x9857127d6987a177d87c13d2dfdaa771bf625a69
Transaction: 0x74a19463e3cc1d131a92599f2ff28effe13064d7c7480c851e7249708de40e3c